A pineapple can have any subnet it wants. Also I have multiple subnets that start 172.16.xx.xx
you must be leet haxor
172.16.0.0/12 is a valid prefix for private networks. In fact, you get more hosts than 192.168.0.0/16, but less than 10.0.0.0/8.
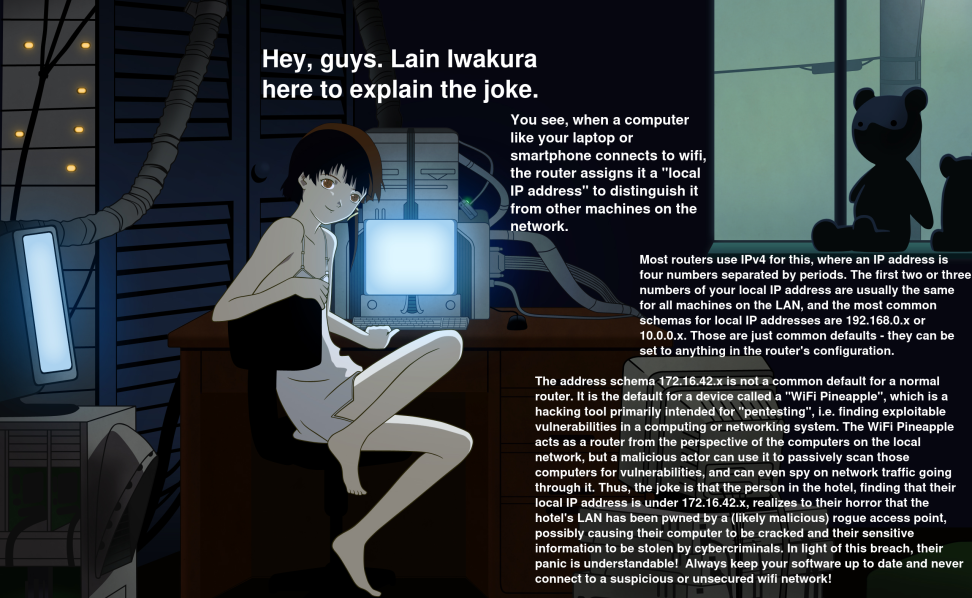
Yeah, it’s not that it’s not valid for private networks, it’s that 172.16.42.x is common for WiFi Pineapples
Every “well ackqually” person in this thread is insufferable
IDK, I find them quite sufferable and in fact I’m learning something from this thread.
Can’t argue with that, I guess
deleted by creator
It’s not that it’s on the 172.16.0.0/12 range. That’s totally normal and used for all kinds of stuff.
It’s that it’s in 172.16.42.0/24 which is the default dhcp settings for a wifi pineapple. It’s the /24 mask given on the .42 that’s a little suspicious because that’s not a common range for anything else.
Being assigned one of those specific 253 hosts with that subnet mask would definitely make me think twice.
It’s the /24 mask given on the .42 that’s a little suspicious because that’s not a common range for anything else.
Well now I know. I operate a ton of /24 subnets in the 172.16.0.0/12 scope. Technically I could fit them in the 192.168.0.0/16 scope, but I have lots of students connecting SoHo wifi-routers to the subnets, and this way it’s pretty easy to tell, if someone put the WAN cable in a LAN port when people are getting 192.168.1.0/24 DHCP offers.
but I have lots of students connecting SoHo wifi-routers to the subnets, and this way it’s pretty easy to tell, if someone put the WAN cable in a LAN port when people are getting 192.168.1.0/24 DHCP offers.
I use 172.31.254.0/23 on my WiFi router. I guess I’d confuse you. /23 to just separate it nicely into 2 /24 blocks.
172.31.254.0/24 range is for manual assignments and 172.31.255.0/24 range is given out by DHCP.
I do not need that many IPs, it’s just for convenience.I chose this range because of my school as it uses 192.168.0.0/16 range.
To help mitigate my possible mistakes when connecting to school network, I set the DHCP lease time to just 5 minutes.172.31.254.0/24 range is for manual assignments and 172.31.255.0/24 range is given out by DHCP. I do not need that many IPs, it’s just for convenience.
I do similar for my home network, mostly for a combination of future proofing and ease of use.
Realistically it would probably make more sense to segment it with more networks, but I’m only going to go so far with complexity for my home production
could calyx vpn save you from a wifi pineapple?
Isnt it also for docker?
deleted by creator
Wtf is with the “…” Explain why pls.
deleted by creator
It’s just one of many private ranges.
Sure, it’s one of many, but how often do you see that specific (42) block used? I honestly don’t think I ever have, outside of a pentest lab. The 172.16.42.0/24 (not just any 172.16 like you’re saying) block is the default for a WiFi Pineapple. Any other range is usually ok, but the 42 on a /24 granting WAN access specifically would make me (and most people who actually know what a WiFi Pineapple is) avoid that network.
Saying 172.16.0.0/12 is usually for pentesting scummy thing is very misleading…Saying it’s dangerous is like saying every websites using
.xyzdomain is dangerous(which makes little more sense than this, btw)You clearly don’t know what a WiFi Pineapple is, because we’re zeroing in on the 42 and you liken it to the entire 172.16 block. And linking every .xyz domain to a specific block (42) that is used by default for a pentest device is even more misleading.
deleted by creator
deleted by creator
There’s nothing at all suspicious about the 172.16.0.0/12 address block.
Correct. However the 172.16.42.0/24 block is the default for a WiFi Pineapple. Any other range is usually ok, but the 42 on a /24 specifically would make me (and most people who actually know what a WiFi Pineapple is) avoid that network.
You mean op’s waifu was wrong?
Please use a VPN anyway, as if hotel WiFi is secure lmao
HTTPS solved much of the security issues of untrusted networks. As long as you’re not doing banking or whatever, you should be fine without a VPN.
Why would banking be an issue? I get that its a target, but I really would expect a bank to take care of their TLS.
Also i would expect banks to use some sort of 2FA where you have to manually confirm any transaction on your mobile device, or enter a code generated from there into your computer.
No security measure is perfect. When doing security-sensitive things, it’s better to wait when you’re home on an uncompromised network.
But yes, the chances of something happening is very small, even when using an unknown network.
It should be fine as long you don’t click through any SSL errors. And something like a bank should have HSTS enabled, meaning your browser will refuse to load the site if there’s an SSL error.
They don’t let me choose a password longer than 6 characters. I don’t assume anything about my bank’s security.
Personally I do a Tailscale tunnel to my home network, if nothing else but so that services don’t log a hotel IP
Public WiFi is just PvP enabled
[x] Client isolation on
This is now a safe zone
The only part of this I didn’t immediately realize is the wifi pineapples default IP range.
From now on, I’m going to set that as my clients default public IP range to troll anyone who knows.
really start to worry when it’s
169.254.0.x…That just means the
DNSDHCP is disabled.Edit: words
-
“The hotel’s free WiFi is really fast”
-
“the DNS is disabled”
-
That is not what that means, it means there’s no dhcp on that network segment.
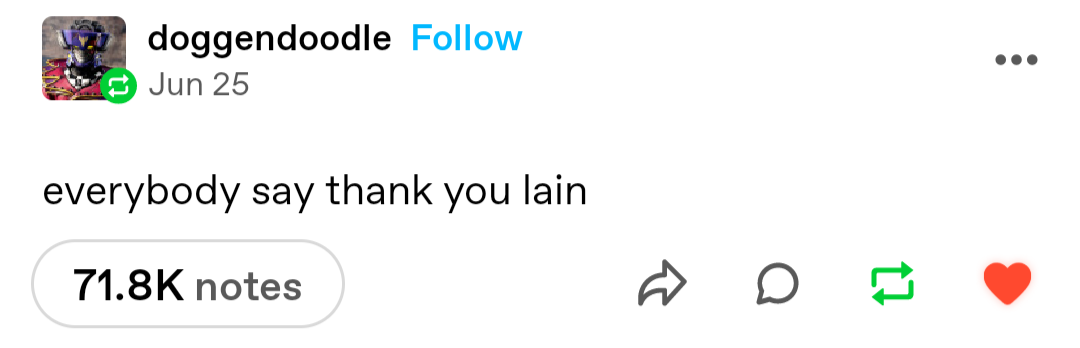
In my defense, whenever there’s a networking issue, it’s always DNS related.
The three stages of grief:
- It can’t be DNS
- There’s no way it could be DNS
- It was DNS
DNS being down is why the DHCP server didn’t start ;)
I can totally see dnsmasq causing this sort of thing.
If there isn’t DHCP and you device isn’t set for a static IP, would it even connect?
So, no… but also yes.
You’re correct that it’s unlikely that the device connecting to the network would be able to reach the outside Internet, but it would still be able to reach any local resource to itself, which is to say any other device which is in its network segment and also in the same state (DHCPless) that it is, via what’s referred to as a link-local address. These are in the 169.254.x.x/16 or fe80::/10 space and allow devices to self-assign addresses independent of upstream connectivity for communication on the local network segment. Usually, these aren’t useful, but these address are consistent, and can be used to directly contact known local hosts from your machine without DHCP. As to whether or not they can reach upstream hosts in this state, the answer is ‘probably not’, but that’s not the same as what you said.
*connects to pineapple
*sets subnet to 10.0.0.0/16 so I don’t have to type a yee yee ass class B/C address everytime I wanna do something with an address
Or
*connects to pineapple
*Sets subnet to same as target network so paranoid user doesn’t realize he connected to evil twin
Always do transparent tunneling with selective MITM, lol
(not gonna help script kiddies any more than this either, lol)
sets subnet to 10.0.0.0/16 so I don’t have to type a yee yee ass class B/C address everytime I wanna do something with an address
Personally I find 172.16.0.0/12 addresses are easier for me to quickly type accurately than any other private range. 192.168.0.0/16 is just too many similar-but-different digits, and 10.0.0.0/8 is too many similar/the same digits before I get to the digits I actually care about, so both are more error prone for me
thank you lain
also omw to set up my dhcpv4 server to use that network whenever I create a hotspot
So I guess I must be a leet haxor because of all the businesses I configured for the 172.x space because 192.168.x space was too small and 10.x space was way the hell too big.
wdym too big? That’s what subnetting is for.
I know what subnetting is for. That’s why I know which RFC range to use. I’m talking based on the number of devices and needed groupings, 172 is a good sweet spot where 198.x would be a bit tight and 10.x is complete overkill.
Could you please explain, how 172.x is different “size” than 10.x? Don’t both of those have 255*255*255 spaces?
Edit: Ok, I made ChatGPT explain it to me. Apparently, with 172.x the convention is to only use range from 172.16.x.x to 172.31.x.x because that range is designated for private networks under some internet regulations…
Yeah. Here’s a breakdown of the allocations and their sizes:
- 192.168.0.0/16 - 65,536 addresses
- 172.16.0.0/12 - 1,048,576 addresses
- 10.0.0.0/8 - 16,777,216 addresses
Most home applications only need a single /24 (256 addresses) so they are perfectly fine with 192.168.0.0/24, but as you get larger businesses, you don’t use every single address but instead break it out by function so it’s easier to know what is what and to provide growth in each area.
But tbh, I still don’t see why you can’t just use 10.x but only as many subnets as you need.
I know jack shit about networking, but I’ve set up OpenWrt routers a couple of times, and set my home network to 10.99. because that was suggested by a ZeroTier tutorial and I thought that’s cool.
You’re technically correct, you can use any of them. It’s honestly just a matter of preference.
For bigger networks, I always went with 10.0.0.0/8 for endpoints, 172.16.0.0/12 for servers and other back-end services, leaving 192.168.0.0/16 for smaller networks like OOB IPMI (eg HP iLO, Dell iDrac) services, cluster heartbeat connections, and certain DMZ segments.
That’s doable too. A lot of people don’t realize you can route all of those together. It’s even more fun as technically you can route private addresses across public links if you own both ends of the link. Used to see that done at a large ISP to route their internal network and it’d pop new networking admins minds.
ETA: I would use 192.x IPs for unrouted subnets like heartbeats or iSCSI.
Common to see big businesses with multiple locations using P2P VPN binding together all sites like one big LAN. Perhaps not ideal from a security standpoint to have the client network so flat, but eh 🤷
Usually a handful of extra important servers are behind an extra layer of firewall rules and/or on a different VLAN with limits on what devices can connect to them.
My current work acquired a company with a very poorly provisioned IT department. Their networks all happen to be in the low 192.168.0.0/16 so users VPNing in often end up with wonky IP conflicts. I’ve heard warnings about similar when selecting subnet ranges, so I just stick with low 192.168.0.0/16 ranges for home networks from which I might potentially VPN into a network I don’t control, and I use 172.16.0.0/12 or 10.0.0.0/8 at work as needed and as aligns with our wider topology.
I will also add that I encountered some fun challenges at a small bank I worked at where they clearly under-planned their network and carried a bunch of wonky configs as vestigial networking adaptations as they grew. They did do a cool thing where they made each branch its own /24 subnet so you could tell at a glance exactly what branch someone was connecting from, plus branches could theoretically limp along with an ISP outage, but they didn’t the extra steps of setting up edge servers so the end result was a full branch outage during an ISP outage
Thank you, Lain.
Does this matter if the traffic is encrypted, such as an https website instead of http? Like, really how often is internet traffic unencrypted?
Yes, back when I was playing around with my WiFi pineapple there were a wide variety of tricks to break SSL authentication without it being obvious to users. Easiest was to terminate the SSL connection on the pineapple and re-encrypt it with a new SSL cert from there to the users browser, so to the user it looked like everything was secure but in reality their traffic was only encrypted from them to the pineapple, then decrypted, sniffed and re-encrypted to pass along to the target websites with normal SSL.
Man in the middle attacks really do give the attacker tons of options
That kind of ssl interception would normally be quite visible without your client device having the pineapples cert in your devices trust store, or am I wrong?
I’m sure a lot has changed in 10 years ago so this won’t be relevant today, but back when I was last playing with this, sslstrip was the tool I was using on the pineapple to enable SSL mitm attacks - https://github.com/moxie0/sslstrip
I’d imagine there are new techniques to counteract new defenses - this stuff is always cat & mouse
Not often. For web browsing - and the majority of apps - your session is encrypted and certified. Breaking SSL is possible but you’ll know about it due to the lack of certs.
Thank you lain.
Thank you Lain.
Thank you, Lain