

Too scary, I couldn’t check it for content. I didn’t want to get nightmares.


Too scary, I couldn’t check it for content. I didn’t want to get nightmares.


Can’t agree more.
I’ll add, from a organisational risk perspective, a government should ensure its not locked into reliance on corporations. There’s certainly an assumption especially in the government’s I work in, Microsoft 365 has no viable alternative. Yet that itself should be warning for the ACSC or signals directorate invest in open code such that if the provider aligns with a country you change positions on, you can fork your code, tender off its continued support to new maintainers, and continue on.
Well, I know that ultimately nobody will get in trouble even if fears became reality. Everyone will put up their hands and say “we couldn’t see this coming and we had no alternative so there’s nothing that could have been done to prevent it.”. It’s just a disappointment that it becomes a missed opportunity for taxpayer investments to be invested, instead of lost to corporate fees straight overseas.
It’s dangerous making conclusions from big assumptions.
Is the kind of reasoning that leads to bias.


That’s why your school got it for pennies.
That’s why Apple sells at near cost to schools.
Walk into the garden, don’t mind the walls, enjoy your stay, you won’t want to leave.
My caption to this could have been “A self fulfilling prophecy”.


“Starry night” on one side, “the scream” on the other. But only if you can get the number plate “Van Go”.
Is that different from this one I remember watching years ago? https://youtu.be/OZzIvl1tbPo
Note I’m not really… Good at math nor really understand it.
I’ll still watch an entertainer and someone good at what they do for entertainment either way.
In my 20 years of outsource IT career I’ve helped lots of business moguls with their personal home mail servers, since I already support their business IT. This doesn’t mean it’s easy, it means they’ve got money to ask someone to do it.
I’m going to tell you, it’s all nice and easy if you understand servers, backup, networking, dns, and security. If you don’t, you’ll probably get it working, for a while, until it doesn’t.
Why do you pay IT if it’s already working? Why do you pay IT if it’s not working?


Wow I read through the blog post and though I’m not a developer I’ve compiled and built Linux packages and operating systems in the past so now I want to fly home and give your script a go myself.
I enjoyed your write up. I can’t comment on programming, but I enjoy a good journey and story.
My final takeaway is your image. I’ll keep it in mind. Interesting!


Make a YouTube on it and I’ll watch it. I’m not a coder though. But benchmarking and debunking is interesting. Either way it goes. Clear or complex the results come out it’ll be interesting.


Yes but they’re hoping a percentage of people don’t go looking for news that their game has been removed and they need to take action to get a refund.
They remove it from the store automatically, but don’t refund automatically.
Though I bet there may be an argument that the payment platform being Apple means it’s opaque to square, it’s still always customers losing. Even if it’s just a percentage.


Jesus fucking christ.
Thanks for the thoughtful reply. I’m extra curious to watch that video later
Thank you, I wouldn’t have chucked this onto a watch later without you specifically noting it wasn’t a FJ video.
Tbh I didn’t think fj would be disliked around here. I’m personally of the opinion that he’s a dochebag and I won’t really watch him. But he’ll take on a fight and publicise problems that should be brought to light. But like any comedian, his job is entertainment and he doesn’t entertain me.
I assume I’ve just missed some scandals. As opposed to my shallow depth dislike of him as a human from internet vibes.
What the heck is my Tuesday night doing posted here?
I’m just saying, nobody in Australia will shed a tear if she stopped existing.


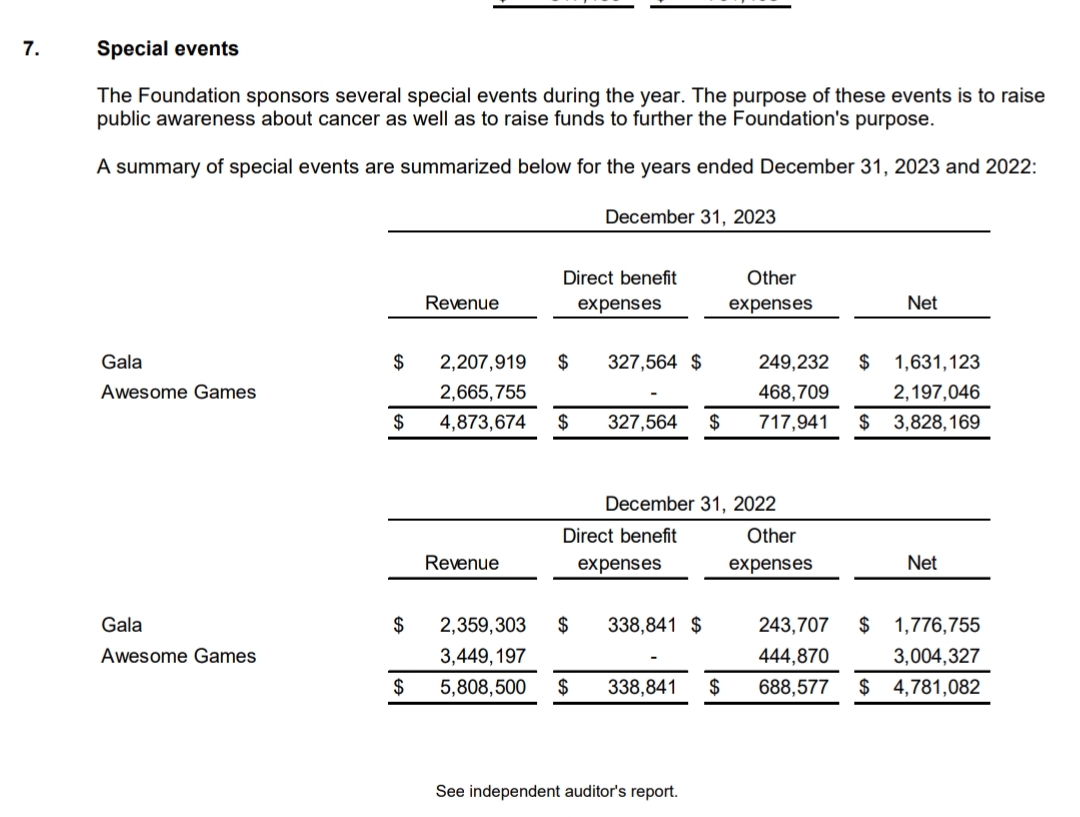
The charity is real, and it took me about 2 minutes to search for their 22-23 audited financial records here https://preventcancer.org/about-us/financials/financial-statements-and-990-forms/
If you go to page 16 you can see the event notes for AGDQ for those two years.
I spent an additional couple of minutes using the propublica lookup. https://projects.propublica.org/nonprofits/organizations/521429544
If you didn’t learn it only for this project, that cost is already sunk regardless.
Either way the post itself contains the answer for those who haven’t already sunk that cost.
Take down his mates, and you’ll leave him out on a limb.