Source Link Privacy.

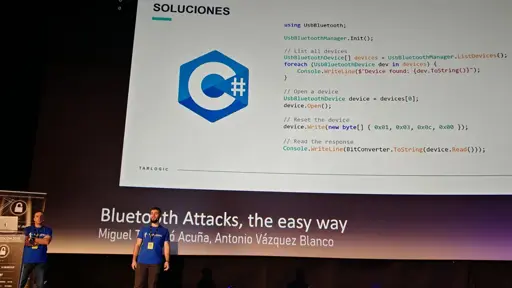
Tarlogic Security has detected a backdoor in the ESP32, a microcontroller that enables WiFi and Bluetooth connection and is present in millions of mass-market IoT devices. Exploitation of this backdoor would allow hostile actors to conduct impersonation attacks and permanently infect sensitive devices such as mobile phones, computers, smart locks or medical equipment by bypassing code audit controls.
Update: The ESP32 “backdoor” that wasn’t.


It’s not a backdoor, it’s a jailbreak. Sounds like they left the debug functionality enabled but just undocumented.
Edit: They’re undocumented HCI commands, that’s the protocol the host (aka CPU) uses to talk to the chip, not a remote device.