If you visit a popular community like /c/[email protected] with your web browser, the images shown are hotlinked from the Lemmy instance that the person posting the image utilized. This means that your browser makes a https request to that remote server, not your local instance, giving that server your IP address and web browser version string.
Assume that it is not difficult for someone to compile this data and build a profile of your browsing habits and patterns of image fetching - and is able to identify with high probability which comments and user account is being used on the remote instance (based on timestamp comparison).
For example, if you are a user on lemmy.ml browsing the local community memes, you see postings like these first two I see right now:
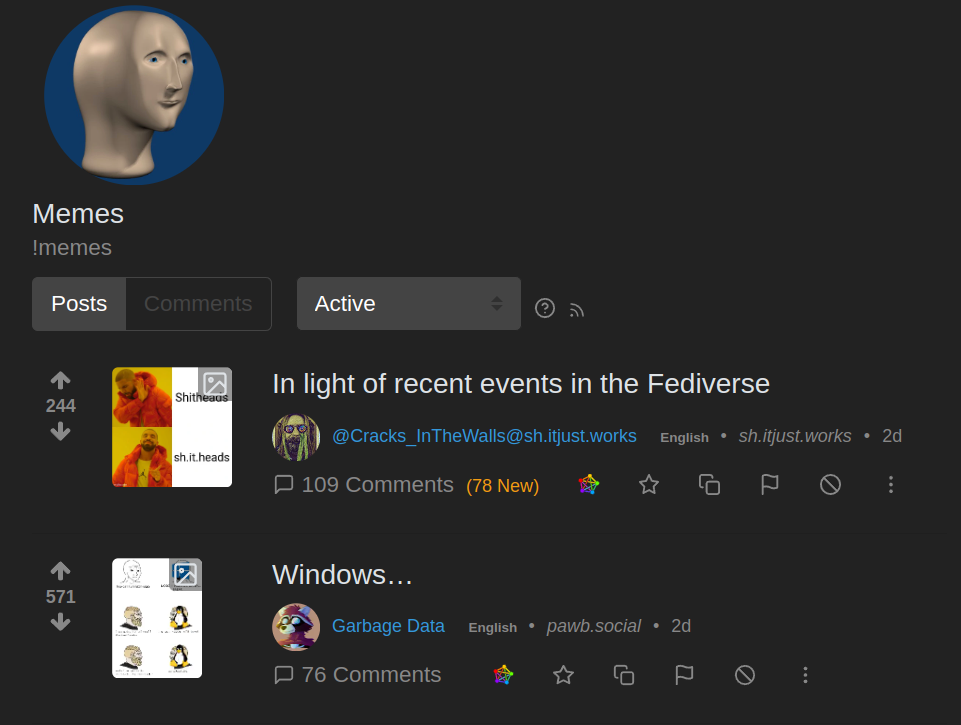
You can see that the 2nd one has a origin of pawb.social - and that thumbnail was loaded from a sever on that remote site:
https://pawb.social/pictrs/image/fc4389aa-bd4f-4406-bfd6-d97d41a3324e.webp?format=webp&thumbnail=256
Just browsing a list of memes you are giving out your IP address and browser string to dozens of Lemmy servers hosted by anonymous owner/operators.
You can trust that I’m too incompetent to actually access that data in any meaningful way, but idk about some of you real tech knowers.
This applies to any website. by visiting the website you give them your IP. the only way to mitigate this is to use a VPN.
Big instances surfing up content from smaller instances is invariably going to cripple them unless larger instances start locally caching that content.
A “solution” to this might be for lemmy instances/apps to have the option to “load remote images” the way e-mail providers do. So I have to actively click to load the images. Could even be done per subscription, so I could declare that I just want everything loaded when I see lemmy.ml/c/pics but not in general, where I usually want text.
IP Address isn’t extremely precise, and I always run on the latest version of whatever browser I’m on, be it Safari or Edge.
deleted by creator
GDPR believes an IP address is a private information. This can be used to mount a legal attack on EU-hosted lemmy instances.
If IP address sharing via hotlinked images, embedded content, etc were breaking GDPR I think the entire internet is breaking it. If I visit a blog, and then click an embedded video or image on that page, then my IP has been shared to someone else while visiting that page. This occurs on the vast majority of the internet.
EDIT: It wouldn’t just be EU-hosted lemmy instances either. GDPR applies to servers outside of EU jurisdiction whenever they’re serving residents of the EU.
Indeed. Most of the web is broken under GDPR’s privacy requirements.
Ever heard of a VPN?
If you use a VPN, the analysis of timestamp probability in logs is still going to reveal that you are likely the user who made x comment at y time. Another lemmy instance you never signed up at can start to look in logs for your comment id: #734995 and cross-reference it to image loading.






